A shared Drive link exposes a sensitive client file.
Public links bypass every password. One wrong setting and your contracts are visible to anyone with a URL.
GOOGLE WORKSPACE SECURITY
Astor runs a structured Google Workspace security program for your business. Regular audits, real fixes, and a weekly cadence that keeps your protection improving over time.
Built for businesses in manufacturing, construction, real estate, agencies, and field services. See what we check.
THE REALITY FOR FAST GROWING BUSINESSES
As you add employees and clients, your Google Workspace gets more complex. We keep it secure so you can move fast without exposure.
Public links bypass every password. One wrong setting and your contracts are visible to anyone with a URL.
Offboarding is easy to forget and expensive to ignore. Access lingers long after people leave.
OAuth permissions are invisible and almost never reviewed. Most small businesses have dozens of unvetted connections.
Without DMARC, anyone can send email that looks exactly like it came from you. Wire fraud starts here.
WHAT WE DO
We focus on the settings, permissions, and access gaps that cause the vast majority of real-world incidents. Then we keep them clean, week after week.
MFA coverage, admin role hygiene, suspicious login patterns. The front door, locked properly.
Former employees and vendors lose access the moment they leave. No lingering ghost accounts.
Public links, overshared folders, sensitive file patterns. We find them before someone else does.
Third-party apps with risky scopes, unmanaged connections, token sprawl. Visibility and control
Anti-spoofing controls that stop fake invoices and CEO fraud before anyone clicks.
Plain-English monthly scorecard. Clear progress. Something you can actually show your insurer.
HOW IT WORKS
Share your domain and rough user count. We reply within one business day.
We send a short checklist and explain exactly what we will review and what we will never touch.
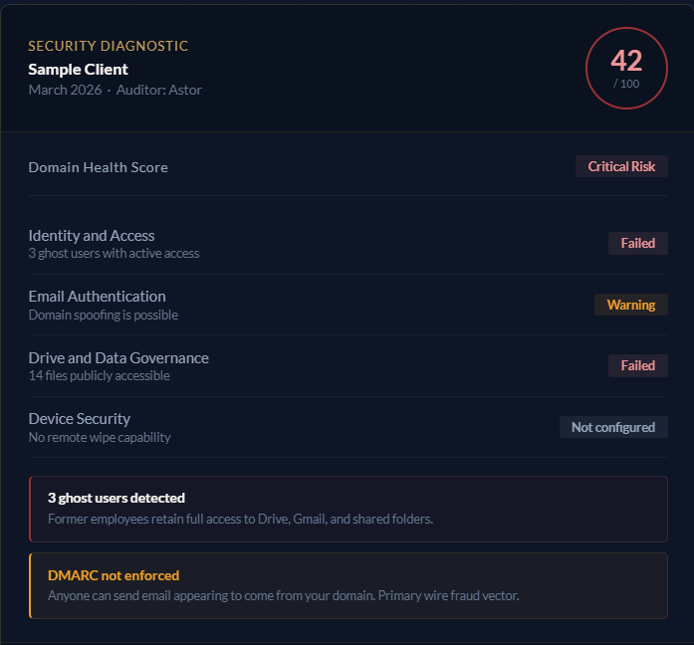
A clean scorecard in plain English with prioritized actions and quick wins.
Fix it once with us, or move into ongoing protection so posture keeps improving.
PLANS
Find your biggest risks and get a prioritized plan to fix them. One-time, no commitment.
Ongoing program protection. Your posture improves every week. Final price based on secured user count.
For regulated teams, complex sharing needs, or rapid growth with higher governance demands.
FAQ
No. We focus on settings, access, sharing configuration, and permission posture. We do not need to open content to find meaningful security improvements.
An admin contact, your domain, and permission to review your Google Workspace security posture. That is it.
Yes. Access can be removed cleanly at any time. We explain exactly what we have and how to remove it before we start.
We do not fix printers, devices, or answer how-to questions related to general user IT support. We focus exclusively on Google Workspace security and governance. That focus is what makes us good at it. If you are looking for full managed services for your business, we refer our clients to MSPs with the appropriate experience.
Most teams move quickly once access is confirmed. We reply to every diagnostic request within one business day with a calendar link and a short access checklist.
GET STARTED
Request a Security Diagnostic and get a clear plan to protect your Google Workspace.